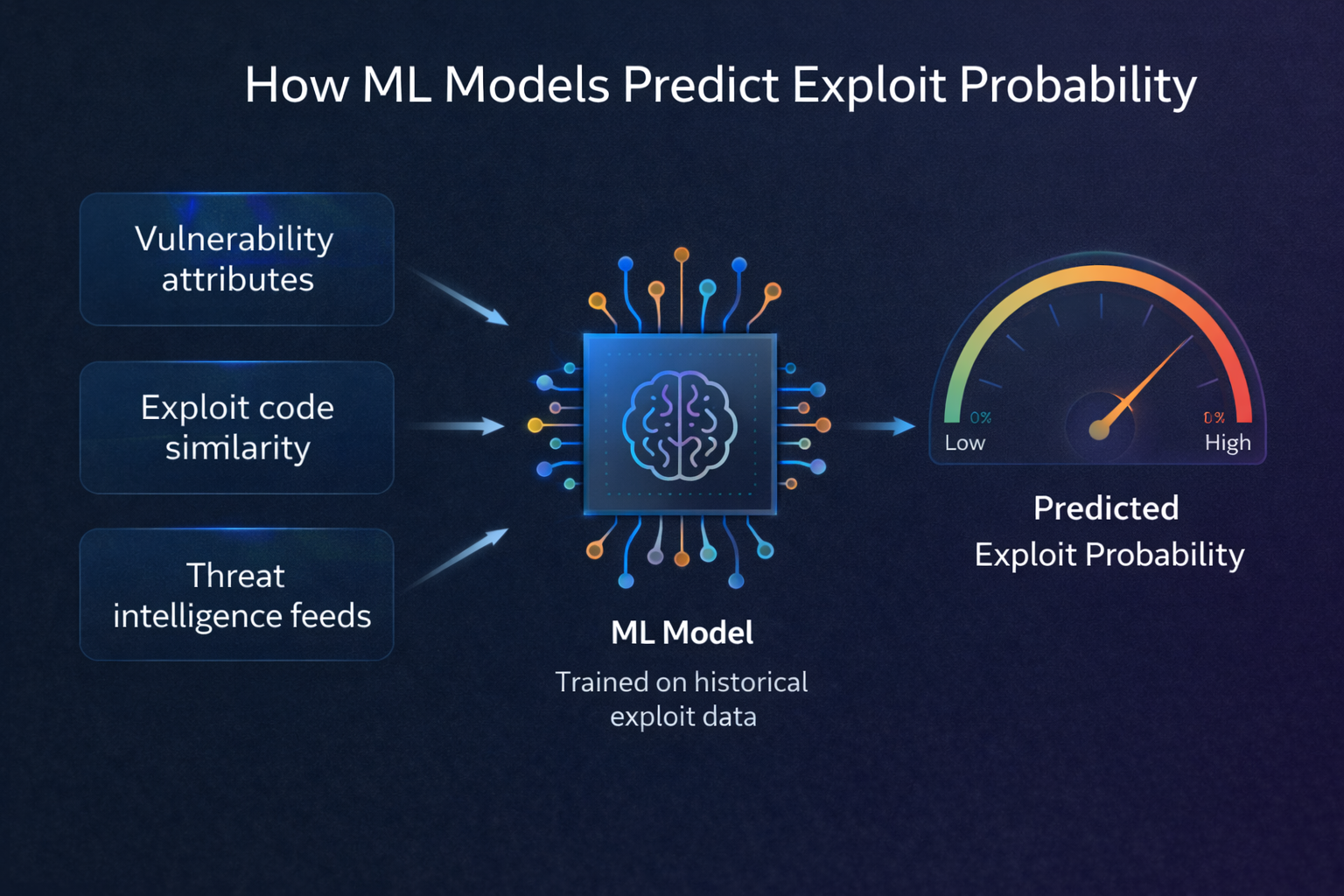
Machine Learning
How ML Models Predict Exploit Probability
A deep dive into the machine learning techniques behind vulnerability exploit prediction.
Nov 28, 2025
6 min read
Read More →