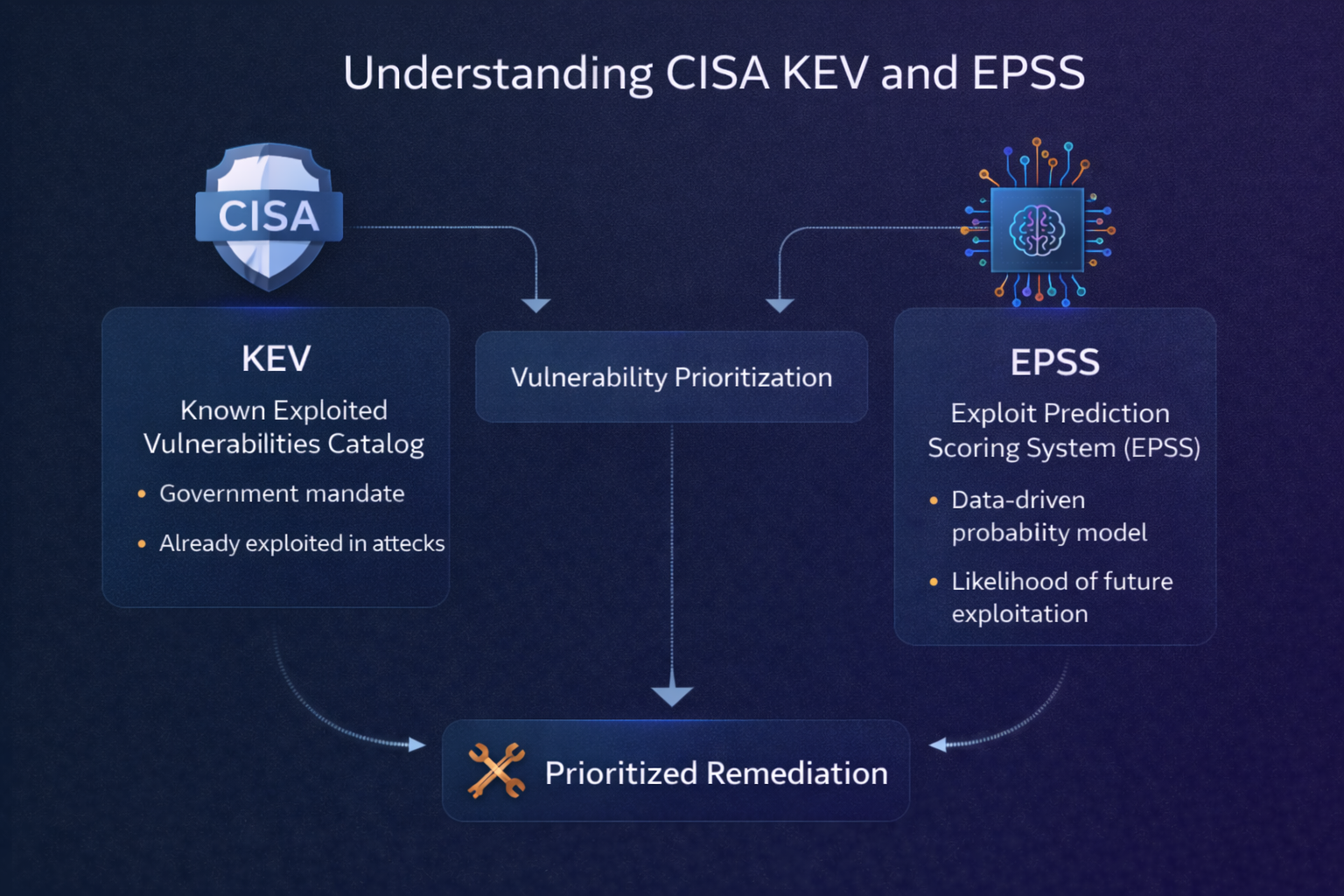
Two threat intelligence sources have fundamentally changed how security teams approach vulnerability prioritization: CISA's Known Exploited Vulnerabilities (KEV) catalog and the Exploit Prediction Scoring System (EPSS). Together, they provide a powerful complement to traditional CVSS scoring by answering the questions that matter most: "Is this being exploited?" and "Will this be exploited?"
CISA KEV: The "Confirmed Exploited" List
Launched in November 2021, the Known Exploited Vulnerabilities catalog is maintained by the Cybersecurity and Infrastructure Security Agency (CISA). It is a curated list of CVEs that have been confirmed as actively exploited in real-world attacks.
What Makes KEV Unique
Unlike CVSS, which rates a vulnerability's theoretical severity, KEV answers a binary question: has this vulnerability been exploited in the wild? Every entry in the catalog meets strict criteria:
- The vulnerability has an assigned CVE ID
- There is reliable evidence of active exploitation
- There is a clear remediation action available (typically a vendor patch)
For U.S. federal agencies, remediating KEV entries is mandatory under Binding Operational Directive (BOD) 22-01, with specific deadlines. But even for private organizations, the KEV catalog serves as an authoritative signal that a vulnerability represents immediate, real-world risk.
KEV by the Numbers
As of late 2025, the KEV catalog contains over 1,100 entries. While that may seem like a lot, it represents a tiny fraction of the 200,000+ total CVEs published. This selectivity is exactly what makes it valuable: if a vulnerability appears on KEV, it has been vetted by CISA analysts and confirmed as a genuine threat.
Key patterns in the KEV data reveal important insights for security teams:
- Speed matters — Many vulnerabilities are added to KEV within days of disclosure. The window between patch release and active exploitation is shrinking.
- Age is no protection — Some KEV entries are for vulnerabilities that are years old, proving that attackers happily exploit old flaws in unpatched systems.
- CVSS doesn't tell the whole story — Several KEV entries have CVSS scores below 7.0. Medium-severity vulnerabilities can and do get exploited when they provide useful attacker access.
EPSS: Predicting Future Exploitation
While KEV tells you what has been exploited, the Exploit Prediction Scoring System (EPSS) estimates what is likely to be exploited. Developed by the Forum of Incident Response and Security Teams (FIRST), EPSS uses machine learning to produce a probability score for each CVE.
How EPSS Works
EPSS analyzes a wide range of features for each vulnerability, including:
- CVSS base score components and vector details
- Age of the vulnerability since publication
- Whether exploit code is publicly available
- References and mentions across security sources
- Characteristics of the affected software and vendor
The output is a probability between 0 and 1, representing the estimated likelihood that a vulnerability will be exploited in the next 30 days. For example, an EPSS score of 0.85 means the model estimates an 85% chance of exploitation within the next month.
Why EPSS Matters
EPSS addresses a critical gap in traditional prioritization. Consider two vulnerabilities, both with a CVSS score of 9.8 (Critical):
- Vulnerability A: EPSS = 0.95 — There's a 95% chance this will be exploited in the next 30 days. Immediate remediation is essential.
- Vulnerability B: EPSS = 0.02 — Despite the Critical CVSS rating, there's only a 2% chance of exploitation. It still needs patching, but it can wait behind higher-probability threats.
Without EPSS, both vulnerabilities would receive the same urgency based on CVSS alone. With EPSS, the security team can make an informed decision about which to patch first.
EPSS Performance
EPSS has been independently validated and shows strong predictive power. The model is updated daily, incorporating the latest threat intelligence data. Research has shown that using EPSS in combination with CVSS significantly outperforms either metric alone for prioritization accuracy.
Using KEV and EPSS Together
KEV and EPSS serve complementary roles in a modern vulnerability management program:
- KEV = Confirmed threat — Any vulnerability on the KEV list should be treated as an immediate priority. It's not a prediction; it's a fact. Remediation timelines should be aggressive (24-48 hours for internet-facing assets).
- EPSS = Predicted threat — High EPSS scores identify vulnerabilities likely to be exploited soon, even before they appear on KEV. This gives teams a head start on emerging threats.
- CVSS = Baseline severity — CVSS still provides valuable information about the potential impact of a vulnerability. It serves as the foundation, with KEV and EPSS layered on top.
A practical prioritization framework might look like this:
- Tier 1 (Immediate): On KEV list, or EPSS > 0.7 on a critical/internet-facing asset
- Tier 2 (Urgent): EPSS > 0.4, or CVSS >= 9.0 with exploit code available
- Tier 3 (Planned): CVSS >= 7.0 with low EPSS, or medium EPSS on low-criticality assets
- Tier 4 (Scheduled): Everything else, addressed in regular patch cycles
Integrating Into Your Workflow
To get the most from KEV and EPSS, integrate them directly into your vulnerability management tooling:
- Automated enrichment — Every vulnerability detected by your scanner should be automatically cross-referenced against the KEV catalog and annotated with its current EPSS score.
- Dashboard visibility — KEV matches and high-EPSS findings should surface prominently in your security dashboard, not buried in spreadsheets.
- SLA alignment — Map your prioritization tiers to specific remediation SLAs. KEV matches on critical assets get 24-hour SLAs; low-EPSS findings on internal systems get 90-day SLAs.
- Continuous monitoring — Both KEV and EPSS change over time. A vulnerability that was low-EPSS last month might spike after new exploit code is published. Rescoring should happen at least daily.
The Bottom Line
CISA KEV and EPSS represent the most significant advancement in vulnerability prioritization in the past decade. By moving beyond static CVSS scores and incorporating real-world exploitation data and predictive intelligence, security teams can finally answer the question that matters: "Which vulnerabilities are most likely to be used against us, and which should we fix first?"
KEV + EPSS + ML, all in one platform
Exploit Score automatically integrates CISA KEV, EPSS scores, and proprietary ML predictions to give you a single, actionable priority for every vulnerability.
Request a Demo