The Exploit Score Process
Three simple steps to smarter vulnerability management
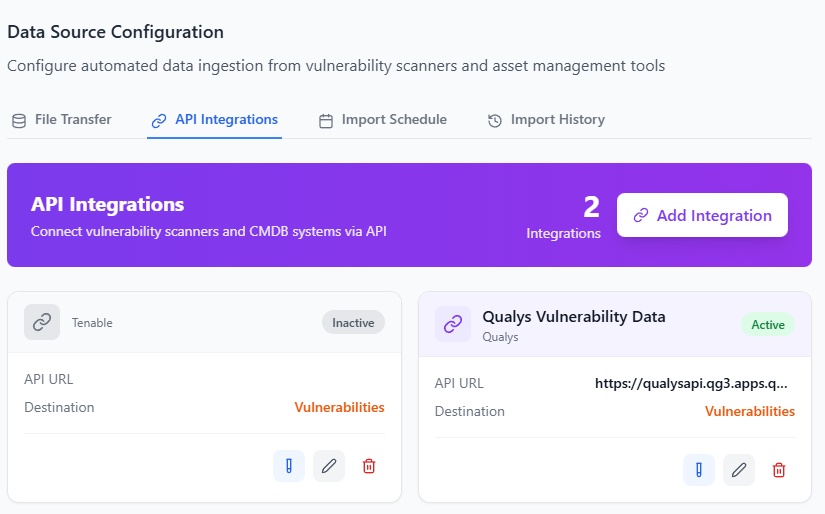
Import Your Vulnerability Data
Connect your existing vulnerability scanners or upload CSV files. We support all major platforms including Qualys, Nessus, Rapid7, and more.
- One-click import from major scanners
- CSV upload with smart field mapping
- Scheduled automatic imports of vulnerabilities and asset details
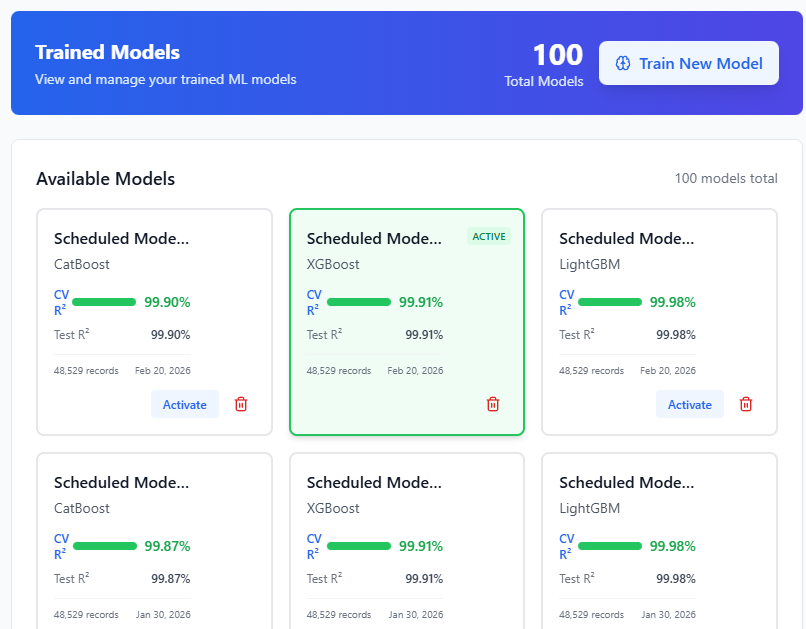
ML Analysis & Scoring
Our machine learning models analyze each vulnerability against multiple factors to predict real-world exploitability and risk.
- CVSS base score analysis
- EPSS probability scoring
- CISA KEV exploit verification
- Industry-specific risk factors
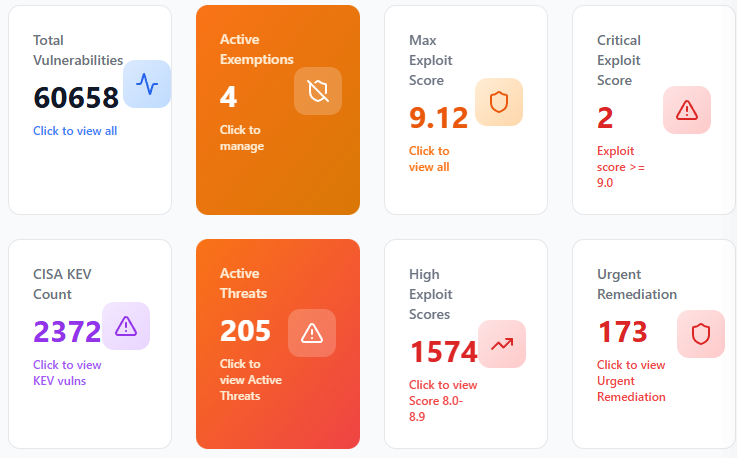
Prioritize & Remediate
Get a prioritized list of vulnerabilities that actually matter. Focus your team's effort on the issues that pose real risk to your organization.
- Prioritized remediation queue
- Risk-based dashboards
- Export reports for stakeholders